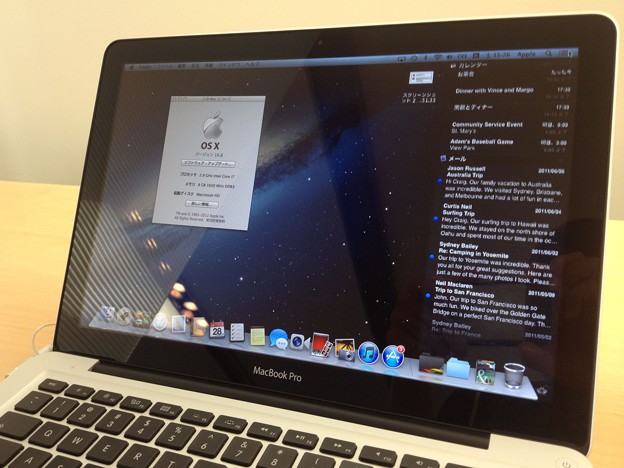
13 Best Features of Mac OS Mojave
The macOS Mojave happens to be the 15th prime release of the desktop operating system by Apple.
Hence, it is packed with a range of new functionalities, features, and new capabilities to look at. In this article, we aim to introduce the top 13 best features of the macOS Mojave.
Mojave 10.14 is compatible with Mac system from mid-2012 or later, just as 2010 and 2012 Mac Pro models that incorporate the prescribed Metal-skilled illustrations cards. On the off chance that you’re shaking one of those systems, then finding what’s going on in Mojave would be of incredible help.
Dark Mode
The Dark Mode is one of the most loved aspects of Mojave. In this mode, all of the native applications such as Xcode, Photos, Calendar, Safari, and more feature darker themes and colors. These colors happen to be very easy on the eyes, which is especially handy for those who spend a significant amount of time working on the mac.
Dynamic Desktop
Have you always dreamt of having a desktop experience which changes as the day progresses? Well, the dynamic desktop of Mojave allows you to experience a desktop that shifts along with the position of the sun based on your location. Essentially, it changes the wallpaper dynamically from the light sky to blue, followed by darker blue as the night approaches.
Desktop Stacks
Do you struggle with a messy background that is full of icons? Well, the Desktop Stacks in Mojave can help you in bringing everything into order. In order to use Stacks, simply right-click on an empty space and choose ‘Use Stacks’.
Screenshot Markups
The Screenshot Markup feature has been on the IOS for some time. Previously, there was a need for a separate app to annotate the screenshots. However, Mojave brings options to quickly make edits after you have taken the screenshots.
Screenshot Utility
There is a new shortcut added to the macOS screenshot arsenal. The Screenshot Utility bar can be brought up by pressing Cmd + Shift + 5. Using this bar, you can screenshot a specific window or the entire screen. On top of that, you can also record the entire screen or a specific area of the screen.
Continuity Camera
The document scanners are dying out as the world moves to the digital side. The continuity Camera on the Mojave makes it easier for you to scan your documents. Essentially, it detects the document in the frame and cuts everything else out while fixing any minor issues.
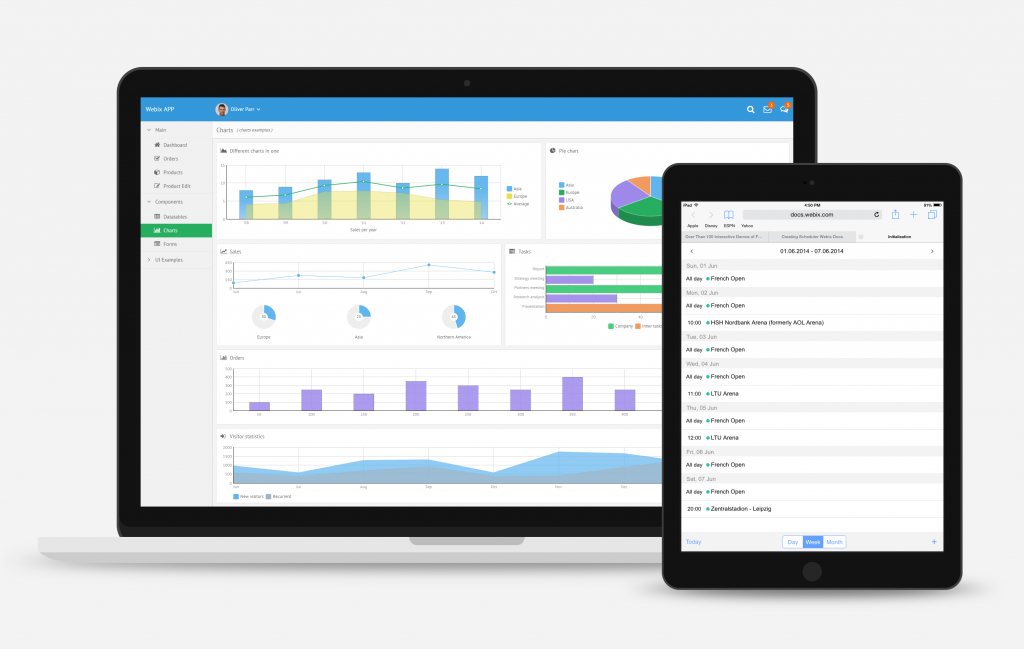
IOS Apps on Mac
After you update Apple Mac to Mojave, you may notice a number of familiar icons in the app launcher. Soon, Apple will introduce a translation layer which will make it possible for you to run the IOS apps on the mac. As of yet, only four supported apps from IOS can be run on the app including Voice Memos, News, Stocks, and Home. Also, it is always good to know about CleanMyMacX Review.
The App Store
The new relationship between the macOS and IOS grows even further due to the App Store. Currently, we can see hints of the mobile counterpart in the desktop app store. The new app store is expected to e much more powerful and easier to move around.
Finder
The Finder has not been ignored in the entire Mojave treatment. Previously, the pictures used to look a little awkward with the Quick Look or Cover Flow in the Finder. The new Gallery View in the Finder has changed this completely.
Other enhancements in Mojave
Mojave carries a range of security improvements, along with improvements in Safari revolving around autofill, creating, and storing passwords.
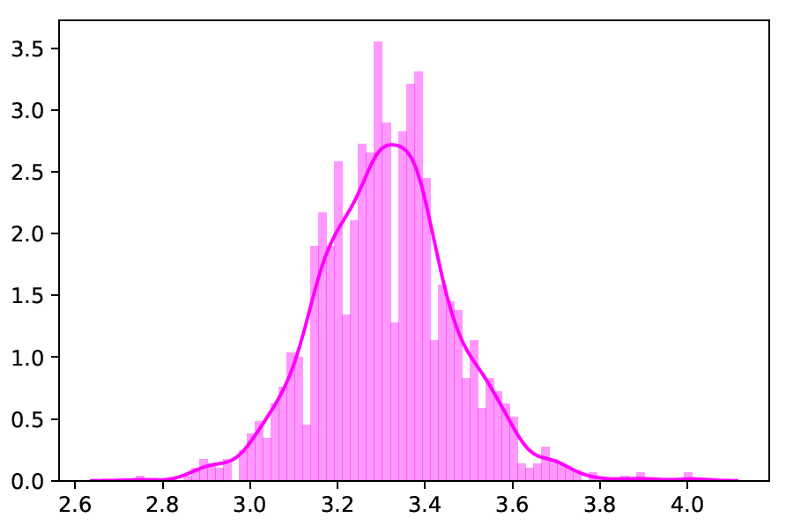
Use APFS to help Fusion Drive

Mojave currently cares more for your files. As guaranteed, Apple made APFS work with Fusion Drive in macOS 10.14 – the unity which empowers you to make, resize and store various volumes of data all the more proficiently on your Mac.
Ask Siri more
The old great Siri gets smarter in macOS Mojave. Not exclusively is Apple’s voice aide lined up with Home Kit, it can likewise enable you to discover saved passwords.
Follow trending topics on Apple News
With Mojave, Apple adds macOS-improved Apple News to the Mac. If you already an active user, you’ll be glad to know that the News application is synced with the iOS version, so you can get speedy access to your preferred sources on Mac directly. Right now, the application is accessible only in a few selected nations like US, UK, and Australia. If you can’t get your hands on Apple News because of geographic restrictions, News Explorer is a good alternative. This convenient newsreader Mac utility is a great device for reading, marking, and sharing content online.
While this is Apple’s greatest and best MAC OS update yet, there are bunches of significant improvements, as well as hidden features in Mojave, which make the upgrade worth it, despite all the trouble. Combine all these tips with the tried-and-trusted applications and you’ll be one happy Mac user.